Difference between revisions of "PfSense"
| (14 intermediate revisions by the same user not shown) | |||
| Line 24: | Line 24: | ||
A hard drive (or SSD) could come in rather handy... | A hard drive (or SSD) could come in rather handy... | ||
<span style="color: rgb(132, 63, 161);" >Coming soonTM... (PromiseTM...)</span> | |||
<span style="color: rgb(132, 63, 161);" >Installing as a VM...</span> | |||
= Install pfSense = | = Install pfSense = | ||
| Line 46: | Line 50: | ||
= Initial Configuration of pfSense = | = Initial Configuration of pfSense = | ||
'''BREAKING NEWS...''' | |||
Apparently, current release sets your networking up to default of WAN using DHCP on the first interface & LAN using 192.168.1.1/24 on the second by default. | |||
If you have more than 2 interfaces, it seems to leave the rest un-configured. | |||
<span style="text-decoration: line-through;">On first boot, pfSense will ask "Should VLANs be set up now [y{{!}}n]?"</span> | |||
*Select your WAN interface | <span style="text-decoration: line-through;">Don't bother...</span> | ||
**bce0 on this test machine (T310) | |||
*Select your LAN interface | *<span style="text-decoration: line-through;">Select your WAN interface</span> | ||
**bce1 on this test machine (T310) | **<span style="text-decoration: line-through;">bce0 on this test machine (T310)</span> | ||
*Verify they're selected properly & say yes. | *<span style="text-decoration: line-through;">Select your LAN interface</span> | ||
*Watch all the "done" messages scroll by (or not... again, your choice...) | **<span style="text-decoration: line-through;">bce1 on this test machine (T310)</span> | ||
*<span style="text-decoration: line-through;">Verify they're selected properly & say yes.</span> | |||
*<span style="text-decoration: line-through;">Watch all the "done" messages scroll by (or not... again, your choice...)</span> | |||
After a moment or 3, you'll see the console menu. | After a moment or 3, you'll see the console menu. | ||
*** Welcome to pfSense 2. | *** Welcome to pfSense 2.6.0-RELEASE (amd64) on pfSense *** | ||
WAN (wan) -> bce0 -> v4/DHCP4: 192.168.0.26/24 | WAN (wan) -> bce0 -> v4/DHCP4: 192.168.0.26/24 | ||
LAN (lan) -> bce1 -> v4: 192.168.1.1/24 | LAN (lan) -> bce1 -> v4: 192.168.1.1/24 | ||
| Line 134: | Line 143: | ||
= Notes & Tips = | = Notes & Tips = | ||
== pfSense with WAN inside a LAN == | |||
<span style="color: rgb(224, 62, 45); font-size: 24pt;" >'''WARNING: This is a potential security hole!'''</span> | |||
If you want to operatea pfSense router entirely inside your local network (i.e.: building a network for installation elsewhere, but testing it locally...) and your local network uses an RFC 1918 address range, you need to allow that sort of addresses on the WAN interface. By default, they are blocked. | |||
At the Web GUI dashboard: | |||
* Interfaces / WAN | |||
** Reserved Networks | |||
*** Un-check "Block private networks and loopback addresses" | |||
<span style="color: rgb(224, 62, 45); font-size: 24pt;" >'''Reverse this if/when your router goes live on the Internet!'''</span> | |||
== If you want to be able to ping your network from the outside, Go into Firewall / Rules / WAN & create a rule to allow ICMP. == | == If you want to be able to ping your network from the outside, Go into Firewall / Rules / WAN & create a rule to allow ICMP. == | ||
| Line 145: | Line 166: | ||
**Just a note, pfSense uses [https://docs.netgate.com/pfsense/en/latest/book/network/understanding-cidr-subnet-mask-notation.html CIDR Subnet Mask Notation] | **Just a note, pfSense uses [https://docs.netgate.com/pfsense/en/latest/book/network/understanding-cidr-subnet-mask-notation.html CIDR Subnet Mask Notation] | ||
Here's a handy [https://www.freecodecamp.org/news/subnet-cheat-sheet-24-subnet-mask-30-26-27-29-and-other-ip-address-cidr-network-references/ Subnet Cheat Sheet] | Here's a handy [https://www.freecodecamp.org/news/subnet-cheat-sheet-24-subnet-mask-30-26-27-29-and-other-ip-address-cidr-network-references/ Subnet Cheat Sheet] | ||
== To allow management access from OUTSIDE your network == | |||
<span style="color: rgb(224, 62, 45); font-size: 24pt;" >'''WARNING: This is a potential security hole!'''</span> | |||
=== Via SSH === | |||
* [https://docs.netgate.com/pfsense/en/latest/recipes/ssh-access.html# Turn on SSHD] | |||
* Create a firewall rule allowing SSH from outside | |||
** <span style="text-decoration: underline;">'''In the Web UI:'''</span> | |||
** Firewall > Rules, WAN Tab | |||
** '''Action''': pass | |||
** '''Interface''': WAN | |||
** '''Protocol''': TCP | |||
** '''Source''': The IP address or subnet of the client, an alias containing management hosts/networks, or (as a last resort only) Any | |||
** '''Destination''': WAN Address | |||
** '''Destination port range''': 22 (Or the custom port) | |||
** '''Description''': Allow remote management from anywhere (Dangerous!) | |||
=== Via Web UI === | |||
* Create a firewall rule allowing SSH from outside | |||
** <span style="text-decoration: underline;">'''In the Web UI:'''</span> | |||
** Firewall > Rules, WAN Tab | |||
** '''Action''': pass | |||
** '''Interface''': WAN | |||
** '''Protocol''': TCP | |||
** '''Source''': The IP address or subnet of the client, an alias containing management hosts/networks, or (as a last resort only) Any | |||
** '''Destination''': WAN Address | |||
** '''Destination port range''':HTTPS (Or the custom port) | |||
** '''Description''': Allow remote management from anywhere (Dangerous!) | |||
'''Note:''' If you are messing about with an internal pfSense server, you'll get '''DNS Rebinding Attack''' errors. Fix this by going into <code>System / Advanced / Admin Access</code> & setting an appropriate '''Alternate Hostnames''' entry under <code>webConfigurator</code>. | |||
= Advanced Topics = | |||
* Multi-WAN failover configuration | |||
** From TecMint: [https://www.tecmint.com/how-to-setup-failover-and-load-balancing-in-pfsense/#:~:text=Failover%20is%20a%20type%20of,or%20any%20scheduled%20down%20times. How to Setup Failover and Load Balancing in PFSense] | |||
* Hardware failover configuration | |||
** Netgate Docs: [https://docs.netgate.com/pfsense/en/latest/recipes/high-availability.html High Availability Configuration Example] | |||
* [[Setting up PIA on pfSense & configuring rules to run traffic to specific sites from inside the LAN through the VPN{{!}}Setting up PIA on pfSense & configuring rules to run traffic to specific sites from inside the LAN through the VPN]] | |||
= Some Links = | = Some Links = | ||
| Line 156: | Line 213: | ||
*[https://www.youtube.com/watch?v=8jYibgeAV0Y Whole-network VPN with pfSense Router] | *[https://www.youtube.com/watch?v=8jYibgeAV0Y Whole-network VPN with pfSense Router] | ||
*[https://www.youtube.com/watch?v=bkWJ8Cmn03I pfSense: How to Setup in DataCenter on VM-ware ESXi (Morton Hjorth)] | *[https://www.youtube.com/watch?v=bkWJ8Cmn03I pfSense: How to Setup in DataCenter on VM-ware ESXi (Morton Hjorth)] | ||
*[https://github.com/pfsense The pfSense source code] | |||
[[Category:Network Management]] | [[Category:Network Management]] | ||
[[Category:pfSense]] | [[Category:pfSense]] | ||
[[Category:ServerBuilding]] | [[Category:ServerBuilding]] | ||
Latest revision as of 09:56, 12 August 2025
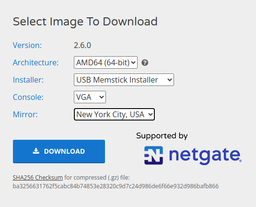
Download pfSense
See that nifty screencap over there on the right?
Look at it again.
It's important...
(You have to start picking options before it'll show you others...)
Stuff it onto a thumbdrive
(really should create command-line instructions for this part)
If working from a Linux Mint machine GUI, right-click & extract the .gz file. Then right-click the resulting .img file & select "Make bootable USB stick".
If working from one of those crappy Windows machines, use Rufus...
If you're playing with a Mac... Yer on yer own for now.
Configure the Hardware
You'll want either a dual NIC or 2 (or more...) NICs.
A hard drive (or SSD) could come in rather handy...
Coming soonTM... (PromiseTM...)
Installing as a VM...
Install pfSense
- Boot your machine from the thumbdrive. (UEFI is just fine...)
- Accept the copyright.
- Select "Install"
- Select "Continue with default keymap" (or, really, any keymap you like...)
- Select "Auto (UFS)
- Choose your disk for the install
- I'd suggest only having one disk in the machine...
- Select "Entire Disk
- Yes... Proceed.
- Select GPT (GUID Partition Table)
- Hit "Finish"
- Hit "Commit"
- Watch the pretty progress screens... (Or ignore it until it's done... Your choice...)
- When you see the "Manual Configuration" screen, Hit "No"
- Hit "Reboot"
- Go back & configure the machine to actually boot from the drive you installed pfSense onto...
Initial Configuration of pfSense
BREAKING NEWS...
Apparently, current release sets your networking up to default of WAN using DHCP on the first interface & LAN using 192.168.1.1/24 on the second by default.
If you have more than 2 interfaces, it seems to leave the rest un-configured. On first boot, pfSense will ask "Should VLANs be set up now [y|n]?"
Don't bother...
- Select your WAN interface
- bce0 on this test machine (T310)
- Select your LAN interface
- bce1 on this test machine (T310)
- Verify they're selected properly & say yes.
- Watch all the "done" messages scroll by (or not... again, your choice...)
After a moment or 3, you'll see the console menu.
*** Welcome to pfSense 2.6.0-RELEASE (amd64) on pfSense *** WAN (wan) -> bce0 -> v4/DHCP4: 192.168.0.26/24 LAN (lan) -> bce1 -> v4: 192.168.1.1/24 0) Logout (SSH only) 9) pfTop 1) Assign Interfaces 10) Filter Logs 2) Set interface(s) IP address 11) Restart webConfigurator 3) Reset webConfigurator password 12) PHP shell + pfSense tools 4) Reset to factory defaults 13) Update from console 5) Reboot system 14) Enable Secure Shell (sshd) 6) Halt system 15) Restore recent configuration 7) Ping Host 16) Restart PHP-FPM 8) Shell Enter an option:
It's ALIVE!!!
Configuring pfSense from here...
At this point, you should be able to connect to the LAN port & point a web browser at 192.168.1.1
This is the Web-UI...
Default login is:
- Username: admin
- Password: pfsense
Change this. Do it NOW!
If you have the WAN port connected to the Internet, you should actually be capable of accessing the outside world right now.
All the fancy stuff
(Coming soonTM... PromiseTM...)
- Configuring Dynamic DNS
- Managing DHCP
- Managing NAT on the firewall
- Multi-Wan Configuration
- Private VPN
- Crap-Stopping with pfBlockerNG
- etc...
Troubleshooting & Repair
Clearing the DNS Forwarder Cache
To clear the DNS Forwarder cache, restart the dnsmasq daemon as follows:
Click Status / Services
Find dnsmasq in the list
Click ![]() , or stop the service using
, or stop the service using ![]() then start again with
then start again with ![]() .
.
Restarting the daemon will clear the internal cache, but the client PCs may still have cached entries.
Flushing the ARP Cache
Click Diagnostics / Command Prompt
arp -d -a
Port Forwarding
- Forwarding Ports with pfSense
- Port Forwarding - Step-by-Step - Demystified - pfSense 2 [SOLVED]
- Open Port Check Tool
- What am I missing on setting this port forward for RDP on pfSense?
Connecting to the VPN machine through the firewall
- SEARCH: bind vnc to network interface
Notes & Tips
pfSense with WAN inside a LAN
WARNING: This is a potential security hole!
If you want to operatea pfSense router entirely inside your local network (i.e.: building a network for installation elsewhere, but testing it locally...) and your local network uses an RFC 1918 address range, you need to allow that sort of addresses on the WAN interface. By default, they are blocked.
At the Web GUI dashboard:
- Interfaces / WAN
- Reserved Networks
- Un-check "Block private networks and loopback addresses"
- Reserved Networks
Reverse this if/when your router goes live on the Internet!
If you want to be able to ping your network from the outside, Go into Firewall / Rules / WAN & create a rule to allow ICMP.
To adjust the size of your subnet on the internal LAN connections:
- Select Interfaces / LANx
- Under Static IPv4 Configuration, change the subnet mask
 (probably from the default /24)
(probably from the default /24)
- Just a note, pfSense uses CIDR Subnet Mask Notation
Here's a handy Subnet Cheat Sheet
To allow management access from OUTSIDE your network
WARNING: This is a potential security hole!
Via SSH
- Turn on SSHD
- Create a firewall rule allowing SSH from outside
- In the Web UI:
- Firewall > Rules, WAN Tab
- Action: pass
- Interface: WAN
- Protocol: TCP
- Source: The IP address or subnet of the client, an alias containing management hosts/networks, or (as a last resort only) Any
- Destination: WAN Address
- Destination port range: 22 (Or the custom port)
- Description: Allow remote management from anywhere (Dangerous!)
Via Web UI
- Create a firewall rule allowing SSH from outside
- In the Web UI:
- Firewall > Rules, WAN Tab
- Action: pass
- Interface: WAN
- Protocol: TCP
- Source: The IP address or subnet of the client, an alias containing management hosts/networks, or (as a last resort only) Any
- Destination: WAN Address
- Destination port range:HTTPS (Or the custom port)
- Description: Allow remote management from anywhere (Dangerous!)
Note: If you are messing about with an internal pfSense server, you'll get DNS Rebinding Attack errors. Fix this by going into System / Advanced / Admin Access & setting an appropriate Alternate Hostnames entry under webConfigurator.
Advanced Topics
- Multi-WAN failover configuration
- From TecMint: How to Setup Failover and Load Balancing in PFSense
- Hardware failover configuration
- Netgate Docs: High Availability Configuration Example
- Setting up PIA on pfSense & configuring rules to run traffic to specific sites from inside the LAN through the VPN